Here’s a perfect guide to help you with Study in the UK
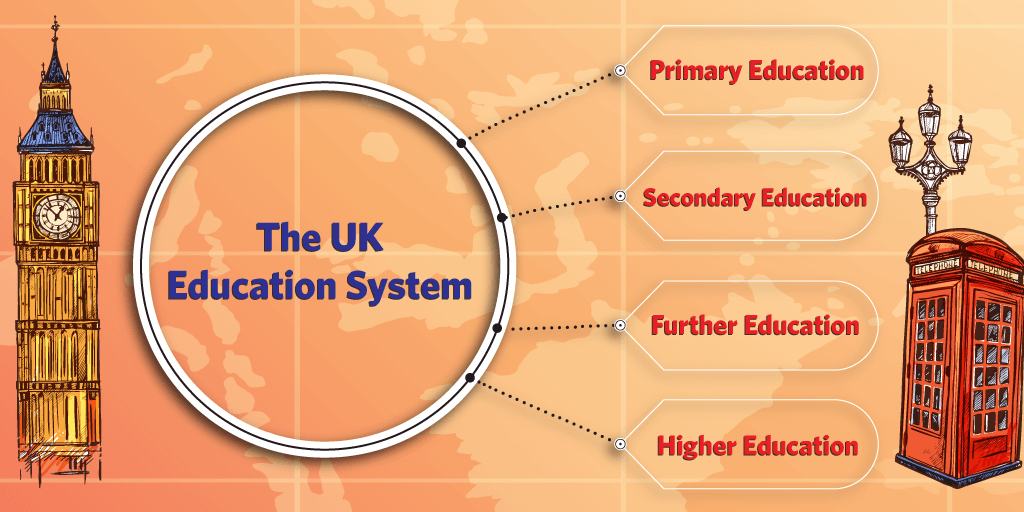
Discover a world-class education in the UK, a renowned global hub for excellence in education and research. The United Kingdom (UK) is home to some of the world’s oldest universities …
Here’s a perfect guide to help you with Study in the UK Read More